Runtime security for cloud/ops AI agents
Runtime guardrails, task-scoped credentials, and an immutable audit trail so your agents ship faster without touching prod.
Built by ex-engineers from HPE and Meta.
Audit trail stays in your VPC.
What Tracehold does, end to end
A single agent action, walked through the full enforcement pipeline.
Agent attempts action
terraform:runs:Apply · module prod-iam
Classified
DESTRUCTIVE · IAM policy change detected
Blast radius scored
Production · 14 resources · high impact
Approval required
Held for human review · credential withheld · 30-min TTL
Evidence logged
Audit entry sealed · trace ID linked · NIST AC-6 tagged
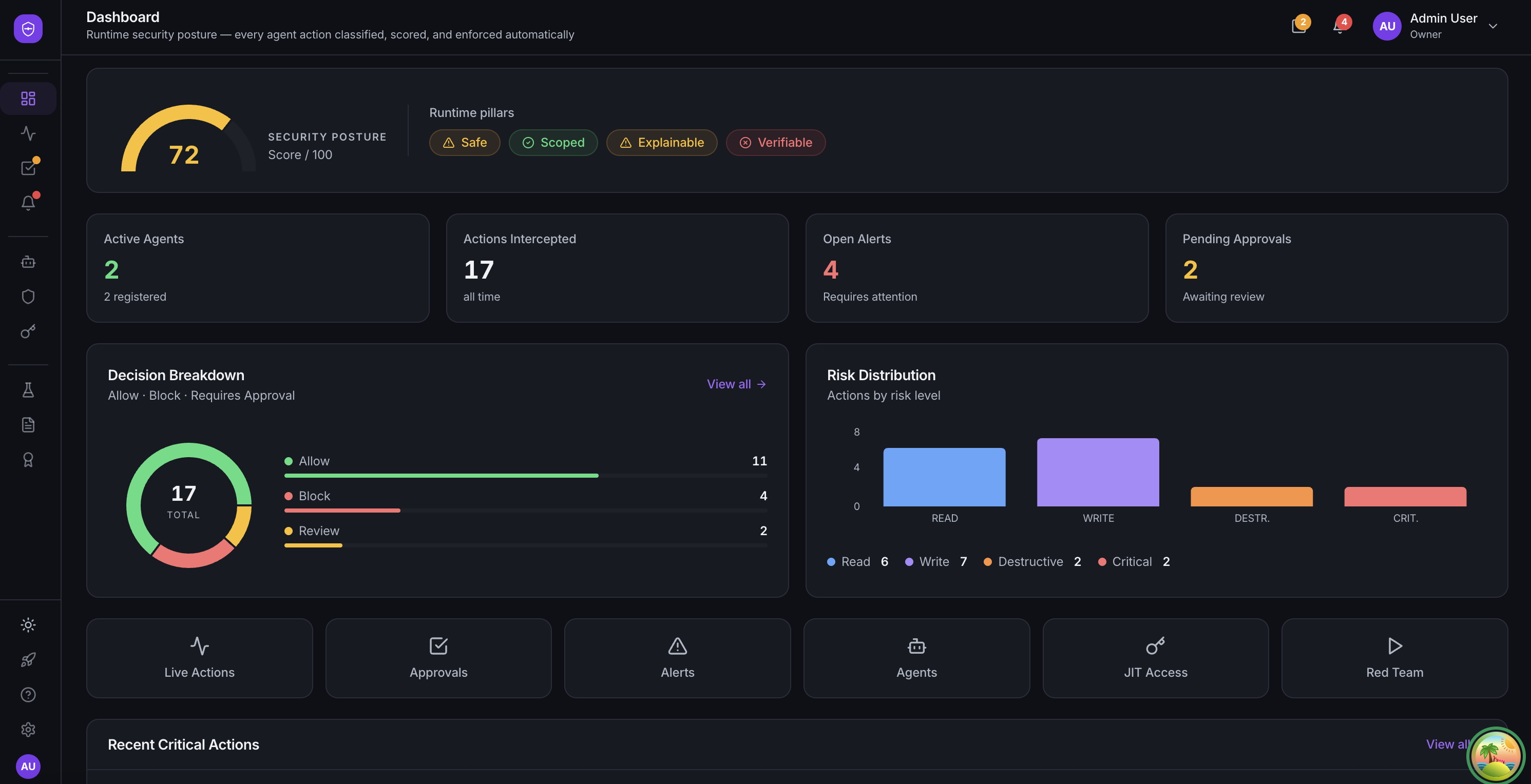
One dashboard for every agent action, classified and scored.
Every agent with real permissions is one prompt away from a CISO's worst day.
Without a runtime gate, a single prompt injection or a bad autonomy loop can become a production incident in seconds.
“Your agent just deleted a production bucket.”
One malformed tool call, no rollback, CISO on the phone.
“Your agent leaked a long-lived IAM key.”
Same key across envs, no rotation, 90 days of blast radius.
“Your audit log has no idea who touched what.”
Auditors ask, 'which agent?' and you have no answer.
Runtime security that meets your agents where they are.
Four pillars behind every Tracehold deployment.
Deploy without rewriting agents
Point your agent at a Tracehold endpoint. Most integrations need no SDK, no wrappers, and no code changes in the agent itself. Tracehold sits between your agent and the cloud.
Works with most agents that can call external tools
Context before action
Every action is assessed against your real environment, not a static rulebook.
Guardrails that explain themselves
Risky actions are paused with a plain-English reason and, where possible, a safer path forward.
Audit-ready from day one
Every decision is permanently recorded and tied back to the compliance controls it satisfies.
Everything you need to run agents in production.
Seven primitives, one platform.
Single enforcement gateway
One enforcement point between your agent and the infrastructure it touches. Every action classified, every action decided, nothing slips through.
Context-aware blast radius
Every action is scored against your real environment, not a generic model. Tracehold knows when a routine call becomes a production incident.
Approvals and action control
Destructive actions can be held for human review with a 30-minute TTL. Decisions are one click, fully contextual, and route to the right owner automatically.
JIT task-scoped credentials
Short-lived credentials issued per task through your provider's native identity federation. They live for the length of the task, then evaporate.
Immutable audit trail
HMAC-SHA256 hash-chained, append-only. Tamper-evident by construction. Export-ready for SOC2, NIST SP 800-53, and OWASP ASI evidence.
Taint tracking + injection defense
Prompt injection, context poisoning, and tainted inputs propagate taint signals through the pipeline. Policies can gate or block any action whose context came from an untrusted source.
AI-powered safer alternatives
When an action is blocked, Tracehold suggests a safer alternative, curated for known actions, intelligently generated for novel ones.
Your agents are re-tested against real attacks on every deploy.
Tracehold replays a library of adversarial scenarios against your real pipeline and catches regressions before they reach production.
Scenarios target Tracehold's enforcement layer itself, verifying that our gating, classification, and audit hold up under adversarial agent behavior, rather than testing your model or your workflow.
Built around OWASP ASI and NIST AI RMF from day one.
Every decision is tagged with the OWASP risk it addresses and the NIST control it satisfies.
OWASP Top 10 for Agentic Applications 2026
Live runtime defenses
- Prompt-injection detectionASI01
- Tainted-input blocking on critical actionsASI02
- Burst and runaway-agent rate controlsASI04
- PII and secret leakage preventionASI06
- Critical-action approval enforcementASI08
- Rogue-agent retry loop detectionASI10
For platform engineers
Connect once. Your agents get safer, you ship faster.
- Point your agent at a URL. In common setups, no SDK or code changes required
- Runs in observe mode on day one, zero production risk
- Hot-reloadable rules, no redeploy to tune
- OpenTelemetry spans on every decision, traceable in Jaeger
For security engineers & CISOs
Every agent action, classified, gated, audited.
- OWASP ASI01–ASI10 anomaly detectors built in
- Immutable hash-chained audit trail, exportable to S3
- Taint propagation for prompt injection and context poisoning defense
- Evidence bundles mapped to NIST SP 800-53 controls
FAQ
Common questions
If your question isn't here, reach out or book a demo.
Does Tracehold sit in the data path between my agent and the cloud?
Yes. Tracehold acts as a single enforcement gateway that intercepts every tool call before it reaches your cloud provider. Every action is classified by risk level, evaluated against your policies, and either allowed, blocked, or held for human approval. You can also run in observe-only mode to start without blocking anything.
Which cloud providers and agent frameworks do you support?
AWS, GCP, Azure, Kubernetes, Cloudflare, Datadog, GitHub, and Terraform ship with 540+ pre-classified actions out of the box. Snowflake, PagerDuty, GitLab, Vault, Pulumi, Confluent, and most REST-API providers can be added through custom classifier rules. Tracehold works with most agent frameworks that can call external tools. Typical integrations take minutes with no agent code changes; complex topologies may need light wiring. We support LangChain, Claude Agent SDK, OpenAI Agents SDK, and CrewAI out of the box. For teams that prefer code-level control, we also offer a Python SDK.
What happens if the Tracehold gateway goes down?
Tracehold supports configurable fail modes per organization. You can choose fail-open (agents continue with logging only) or fail-closed (agents are paused until the gateway recovers). Most production deployments use fail-closed for critical workloads and fail-open for non-critical ones.
Is Tracehold self-hosted or managed?
Both. You can self-host Tracehold in your own VPC so your audit trail and credentials never leave your infrastructure, or use our managed deployment. The entire stack runs on Docker Compose with PostgreSQL, Redis, and an OpenTelemetry collector.
How is Tracehold different from a WAF or prompt injection filter?
WAFs and prompt filters protect the input side. Tracehold protects the output side: the actual cloud actions your agent takes. We classify every tool call by risk and blast radius, issue short-lived credentials scoped to each task, and maintain a tamper-evident audit trail. Think of it as IAM and audit for AI agents, not another input filter.
Does Tracehold align with OWASP and NIST standards?
Yes. Tracehold is built around the OWASP Top 10 for Agentic Applications 2026 (ASI01 through ASI10) and maps every gateway decision to NIST SP 800‐53 controls (AC-6, AU-2, AU-12, CM-5, IA-9, SC-28, SI-7). The immutable audit trail exports as compliance evidence for SOC 2 and NIST AI RMF assessments.
How long does it take to integrate Tracehold?
Typically minutes. You create a connection endpoint in the Tracehold dashboard, select which cloud actions to expose, and point your agent at the URL with an API key. In common setups, no SDK installation, no code changes, and no redeployment are required.
See Tracehold running against your stack.
30-minute demo. We run your real agent workflow through the gateway against a sandboxed copy of your stack.